Kruchten’s 4+1 views for solution architecture
4+1 is a view model designed by Philippe Kruchten describing the architecture of IT systems, based on the use of multiple, concurrent views.
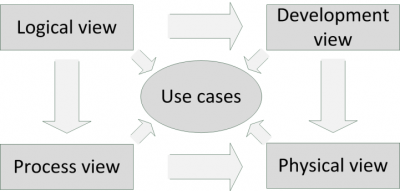
Figure: 4+1 views
The 4+1 views describe a solution from the viewpoint of different stakeholders. The model contains the following views:
- Logical view - this describes the functionality that the system provides to end users
- Development / implementation view - this describes the system from a programmer's perspective and is concerned with software management
- Process view - this describes the dynamic aspects of the system, explains the system processes and how they communicate, and focuses on the runtime behavior of the system. The process view addresses issues like concurrency, distribution, integrators, performance and scalability
- Physical / deployment view - this describes the system from a system engineer's point of view. It is concerned with the topology of software components on the physical layer, as well as communication between these components.
- Use cases - this describes a small set of use cases, or scenarios, the fifth view. They are used to identify architectural elements and to illustrate and validate the architecture design.
Apart from software architecture, the 4+1 view descriptions can be used in infrastructure architecture as well. The 4+1 views define what should be documented and how (4+1 prefers using UML for this). It does not contain a process on how to create the documentation, like the SEI stack does.
This entry was posted on Friday 05 July 2013
 English
English